In celebration of Cyber Security Awareness Month, we’ve rounded up 7 surprising statistics about cyber security you need to know in order to protect your business.

Data breaches rack up costs quickly, including in some surprising areas. The top three are below:
- Increased customer turnover – even the most loyal of customers can lose trust and faith in your business when their data is compromised.
- Lost revenue due to system downtime – Downtime compromises payments, new customer signup, and prospect discovery.
- Increasing cost of acquiring new business due to diminished reputation – new customers will be wary of giving business to companies who can’t protect their data.
As you can see, the costs associated with cyber security pale in comparison to the costs on your business when your customers’ data is compromised. Implementing and utilizing technology with the highest security standards is crucial to the integrity of your data and trust of your customers.
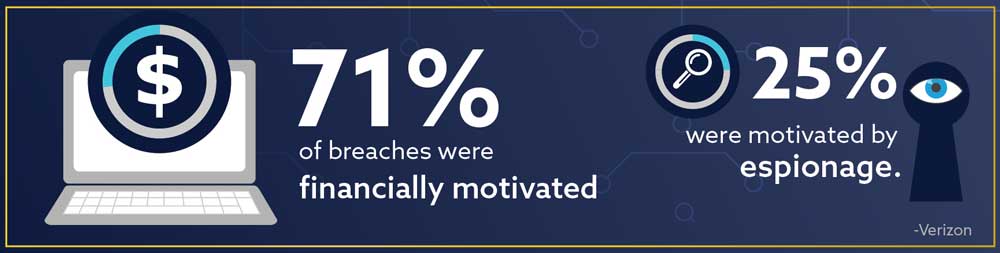
We are all well aware at this point of financially motivated attacks, like ransomware. When ransomware infects your network, your data is held hostage and released for a fee. If you do not comply by a certain date, the cost doubles or your data is permanently deleted or locked. According to McAfee, ransomware attacks grew 118% in 2019.
Espionage, however, might seem like a job for James Bond. Unfortunately, given the highly competitive and often political climate we are in, cyber espionage doesn’t involve a bullet-dodging adventure in the movies, but instead features hackers getting into your network to obtain economic, political, or military gain by stealing your intellectual property.

If you think you’re safe from a data breach because you’re not a fortune-500 company, you’re wrong. Small businesses are often the perfect target for a data breach, because cyber security may not be a priority on an already strict budget. However, according to Verizon’s report, cloud services that offer a myriad of web-based tools, along with the rise of social phishing attacks, are leveling the playing field between large enterprises and small businesses. If you’re not adopting secure cloud technologies and educating your staff on potential threats, you put your business data at risk of a breach.

Not all data breaches are caused by external hackers. Sometimes the bad actors are in your own organization. Take, for example, the recent news where a Tesla employee was offered $1 million to facilitate a cyber attack. Luckily, this employee instead worked with the FBI to catch and prosecute the criminal before any harm was done. Unfortunately, this isn’t always the case.
It’s important to note that not all data breaches are caused with the intent of harm. Human error is inevitable, and it sometimes takes simply copying sensitive information to your home computer to become vulnerable. With remote work becoming the norm, this is especially dangerous as we juggle our personal and business devices in addition to integrating with the Internet of Things (IoT).

The amount of data is increasing, and it’s easy for documents to get copied, deleted, and shared beyond control. When you do not have an efficient and secure information management system in place that restricts and audits users access to documents, you become vulnerable to loss, theft, and overwritten files. Plus, with the cost of replacing a lost or stolen record at $150 per record, it’s worth it to take a deep look at your file permissions structure.1
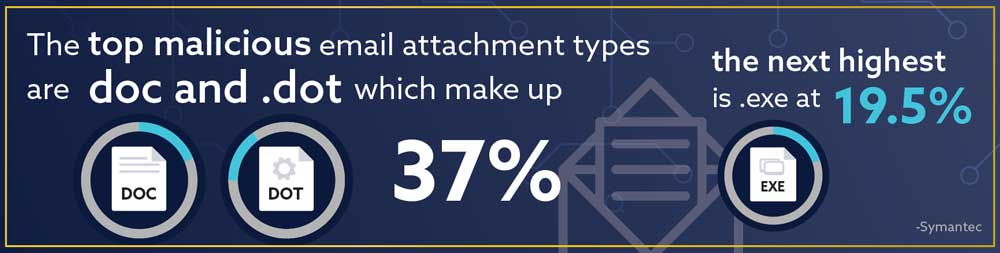
Email and social phishing attacks are the most common types of data breach for large and small businesses, according to Verizon. They often trick users into thinking they’re clicking a link or document they recognize from a reputable company, but instead that click opens the doors for malware designed to infect your system and infiltrate your network. Educating your employees on common phishing tactics and infected document types is a good first step.

The faster you can contain a data breach, the better for your business. Can you imagine the difference 160 days may mean for you and your customers? If you haven’t already deployed security automation within your business, now is the time. No one is 100% safe from a potential data emergency, but having a plan in place while relying on secure cloud technologies could potentially save you millions in the long run.
In 2020, data is still very much at risk. However, your best line of defense is educating employees, using trustworthy technology for security automation (especially in the cloud), and having an aggressive strategy for minimizing the damage done when a breach occurs.
At Digitech Systems, the security of your information is of paramount importance and we are recognized cyber security experts. You can rest easy knowing that your documents are safely protected behind five levels of security. If you want to learn more about our monomaniacal focus on information security, contact us today!
Sources
1: IBM, Ponemon (2020). “The 2020 Cost of a Data breach cost.” (https://www.ibm.com/security/data-breach)
Stats1, 7: IBM, Ponemon (2020). “The 2020 Cost of a Data breach cost.” (https://www.ibm.com/security/data-breach)
Stats 2, 3, 4: Verizon (2020). “2020 Data Breach Investigations Report.” (https://enterprise.verizon.com/resources/reports/2020-data-breach-investigations-report.pdf)
Stat 5: Varonis (2019). “2019 Varonis Global Data Risk Report." (https://www.varonis.com/2019-data-risk-report/)
Stat 6: Symantec (2018). “Internet Security Threat Report." (http://images.mktgassets.symantec.com/Web/Symantec/%7B3a70beb8-c55d-4516-98ed-1d0818a42661%7D_ISTR23_Main-FINAL-APR10.pdf?aid=elq)
Related Links:
Visit the links below to learn more about cyber security.
- Did you know we have an entire page dedicated to Cyber Security? Check it out!
- If you're working remotely, check out this infographic all about telework and cyber security.
- Learn how Real Property Management Vancouver was able to keep their data secure while working remote during the Covid-19 pandemic thanks to ImageSilo® with this case study.
- If you're curious about how Digitech Systems products protect its customers data, check out this infographic on our five layers of security.
